SSH Into Bastion Host and Internal Server In One Command
Quick Background: What is a bastion host?
A Bastion Host is a server that sits between the internet and private network. The bastion host allows access to machines on the private network (usually through SSH) for adminstration or debugging. Typically you want bastion hosts to be IP whitelisted, if possible, to minimize the potential for attacks on the server.
Typical Bastion SSH Workflow
A typical workflow to access servers in a private network such as a private AWS VPC (Virtual Private Cloud) is to SSH into the bastion host and then, from there, SSH into one of the private servers. This requires you to wait for the SSH to connect and then write another command that SSH's into the internal server. While this two-step process is fairly simple, it adds time and typing overhead to an often frequent operation.
Solution
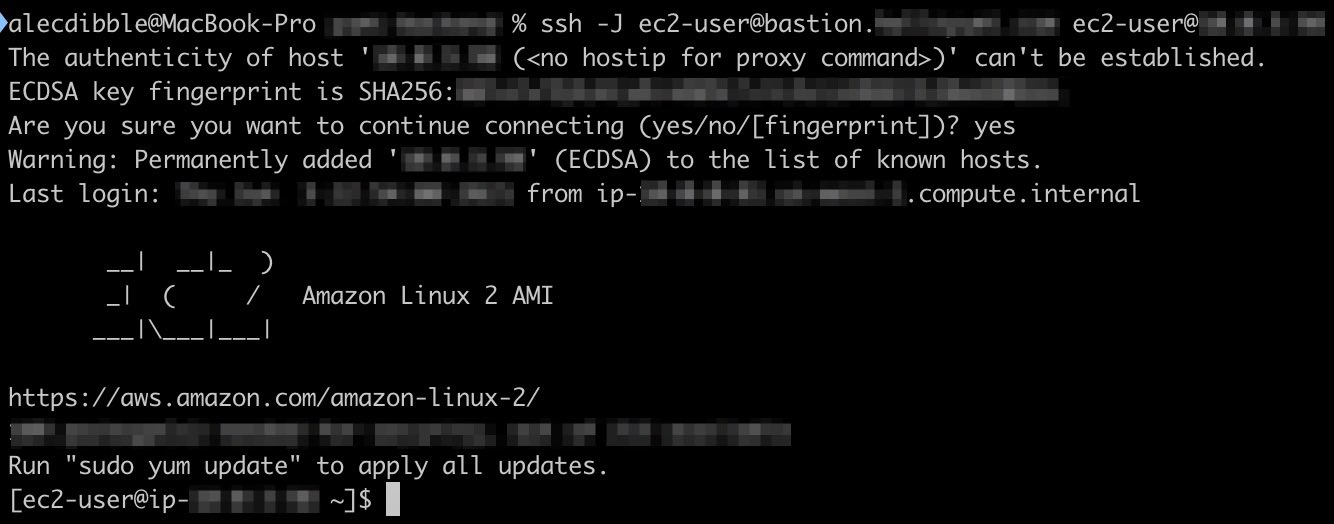
To SSH into a private server from a bastion host (or more generally SSH from Local Machine A into Server C from Server B), here is the command:
ssh -J userA@Server-B userB@Server-C
Note: this command requires OpenSSH version 7.3 or above. To determine your OpenSSH version, type ssh -V in your terminal.
Addendum: Key Files and Improved Security
By default, this command will use the local key file of Machine A (the original machine you are SSH'ing from) for both Server B (the Bastion Host) and Server C (the private network server). This is a better setup then having the private servers accept the Bastion Host's key. If the private servers can accept the Bastion Host key, a compromise of the Bastion Host will give an attacker direct access to the whole private network.
Acknowledgement
Special thanks to this AskUbuntu answer for helping me discover this command.